Snowflake
This guide explains how to create a read-only service account (metadata access only) for Revefi on Snowflake.
Step 1: Create role, user, warehouse and grant account permissions
As a super user, execute the following SQL commands to create a read-only role, a user assigned to that role, and a warehouse for that role.
**Please note: **
Make sure to generate an RSA keypair and copy the public key into the field called RSA_PUBLIC_KEY and store the public and private key securely — you'll save it into Revefi later.
Exclude the key delimiters
-----BEGIN PUBLIC KEY-----and-----END PUBLIC KEY-----when setting the RSA_PUBLIC_KEY in the following script.
During the initial onboarding, Revefi recommends using a MEDIUM size warehouse. After the initial onboarding is complete (typically 1 week) you can revert the warehouse size to X-SMALL/SMALL depending on your query history.
We recommend using Snowflake's worksheet interface to run the snippet. Please copy the code and make any necessary modifications before running it._
-- Use a role with sufficient privileges to grant the below permissions
USE ROLE ACCOUNTADMIN;
-- Configuration
set revefi_username='REVEFI_USER';
set revefi_warehouse_size='MEDIUM';
set revefi_warehouse_name='REVEFI_WH';
set revefi_role_name='REVEFI_ROLE';
SET revefi_db = 'REVEFI_DB';
-- Create warehouse for Revefi's monitoring workload
CREATE WAREHOUSE IF NOT EXISTS identifier($revefi_warehouse_name) WAREHOUSE_SIZE=$revefi_warehouse_size INITIALLY_SUSPENDED=TRUE AUTO_SUSPEND = 60 AUTO_RESUME = TRUE MAX_CONCURRENCY_LEVEL = 32 STATEMENT_TIMEOUT_IN_SECONDS = 1200 STATEMENT_QUEUED_TIMEOUT_IN_SECONDS = 1200;
-- Create the role Revefi will use
CREATE ROLE IF NOT EXISTS identifier($revefi_role_name);
-- Create Revefi's user and grant access to role
-- Note: please provide the RSA public key generated above with the '--BEGIN PUBLIC KEY--' annotation removed, e.g. 'MIIBIjANBgkqh...'
CREATE USER IF NOT EXISTS identifier($revefi_username) RSA_PUBLIC_KEY='<RSA_PUBLIC_KEY>' DEFAULT_ROLE=$revefi_role_name;
GRANT ROLE identifier($revefi_role_name) TO USER identifier($revefi_username);
-- Create a dedicated database for REVEFI to use store query log metadata
CREATE DATABASE IF NOT EXISTS identifier($revefi_db);
-- Grant permissions to use the new warehouse
-- OPERATE allows Revefi to start and stop the warehouse
-- MODIFY allows Revefi to reduce the warehouse size when usage is low.
GRANT USAGE, MONITOR, OPERATE, MODIFY ON WAREHOUSE identifier($revefi_warehouse_name) TO ROLE identifier($revefi_role_name);
-- Grant privileges to allow access to query history and other account level metadata
GRANT IMPORTED PRIVILEGES ON DATABASE "SNOWFLAKE" TO ROLE identifier($revefi_role_name);
-- Grant privileges to allow schema, table, view, procedure and task management on the dedicated database for Revefi
-- Usage on all schemas and db
GRANT USAGE ON DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
GRANT USAGE ON ALL SCHEMAS IN DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
-- Schema management
GRANT CREATE SCHEMA ON DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
-- Table management
GRANT CREATE TABLE ON ALL SCHEMAS IN DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
GRANT SELECT, INSERT, UPDATE, DELETE ON ALL TABLES IN DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
GRANT SELECT, INSERT, UPDATE, DELETE ON FUTURE TABLES IN DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
-- View management
GRANT CREATE VIEW ON ALL SCHEMAS IN DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
GRANT SELECT ON ALL VIEWS IN DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
GRANT SELECT ON FUTURE VIEWS IN DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
-- Procedure and task management (For query log maintenance)
GRANT CREATE PROCEDURE ON ALL SCHEMAS IN DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
GRANT CREATE TASK ON ALL SCHEMAS IN DATABASE identifier($revefi_db) TO ROLE identifier($revefi_role_name);
GRANT EXECUTE TASK ON ACCOUNT TO ROLE identifier($revefi_role_name);
Step 2: Provide metadata access to each database you want to monitor
Please note:
Replace <comma_separated_db_list> with the actual name of the databases you want to monitor
-------------------------------------------------------------------------------
-- Use a role with sufficient privileges
USE ROLE ACCOUNTADMIN;
-------------------------------------------------------------------------------
-- Configuration
-- revefi_role_name: Revefi role to which permissions will be granted
SET revefi_role_name = 'REVEFI_ROLE';
-- database_list: Comma-separated list of database names for Revefi to monitor
-- NOTE: If your database name has special characters, please double quote the name
-- EXAMPLE:
-- SET database_list = 'DB1,DB2';
-- SET database_list = 'DB1, DB2, "prod-orders"';
-------------------------------------------------------------------------------
SET database_list = '<comma_separated_db_list>';
-- Use any existing database name that your current role has access to, this is only used to temporarily create the stored procedure below
SET db_for_procedure='<any_database>';
-------------------------------------------------------------------------------
-- Helper procedure: GRANT all *database-level* privileges for one database
--
-- This procedure grants:
-- - USAGE on the database
-- - USAGE on all schemas and future schemas
-- - REFERENCES on tables/views (all + future)
-- - MONITOR on dynamic tables (all + future)
-------------------------------------------------------------------------------
USE DATABASE identifier($db_for_procedure);
CREATE OR REPLACE PROCEDURE GRANT_DB_PRIVILEGES(db_name STRING)
RETURNS STRING
LANGUAGE JAVASCRIPT
EXECUTE AS CALLER
AS
$$
// Grant usage
snowflake.execute({sqlText: `GRANT USAGE ON DATABASE identifier('${DB_NAME}') TO ROLE identifier($revefi_role_name)`});
snowflake.execute({sqlText: `GRANT USAGE ON ALL SCHEMAS IN DATABASE identifier('${DB_NAME}') TO ROLE identifier($revefi_role_name)`});
snowflake.execute({sqlText: `GRANT USAGE ON FUTURE SCHEMAS IN DATABASE identifier('${DB_NAME}') TO ROLE identifier($revefi_role_name)`});
// Grant table/view references
snowflake.execute({sqlText: `GRANT REFERENCES ON ALL TABLES IN DATABASE identifier('${DB_NAME}') TO ROLE identifier($revefi_role_name)`});
snowflake.execute({sqlText: `GRANT REFERENCES ON FUTURE TABLES IN DATABASE identifier('${DB_NAME}') TO ROLE identifier($revefi_role_name)`});
snowflake.execute({sqlText: `GRANT REFERENCES ON ALL VIEWS IN DATABASE identifier('${DB_NAME}') TO ROLE identifier($revefi_role_name)`});
snowflake.execute({sqlText: `GRANT REFERENCES ON FUTURE VIEWS IN DATABASE identifier('${DB_NAME}') TO ROLE identifier($revefi_role_name)`});
// Grant monitor on dynamic tables
snowflake.execute({sqlText: `GRANT MONITOR ON ALL DYNAMIC TABLES IN DATABASE identifier('${DB_NAME}') TO ROLE identifier($revefi_role_name)`});
snowflake.execute({sqlText: `GRANT MONITOR ON FUTURE DYNAMIC TABLES IN DATABASE identifier('${DB_NAME}') TO ROLE identifier($revefi_role_name)`});
return `Granted DB-level privileges on: ${DB_NAME}`;
$$;
;
-------------------------------------------------------------------------------
-- Procedure: GRANT_SCHEMA_REFERENCES_FOR_DB
--
-- Fixes issues arising due to Snowflake's schema-level FUTURE grants overriding
-- database-level FUTURE grants.
--
-- Logic:
-- - Switch into the selected database
-- - Enumerate all schemas (except INFORMATION_SCHEMA)
-- - If a schema has FUTURE grants defined:
-- → Grant REFERENCES on tables/views (all + future) for that schema
--
-- If no schema has FUTURE grants, this procedure is effectively a NO-OP.
-------------------------------------------------------------------------------
USE DATABASE identifier($db_for_procedure);
CREATE OR REPLACE PROCEDURE GRANT_SCHEMA_REFERENCES_FOR_DB(db_name STRING)
RETURNS STRING
LANGUAGE JAVASCRIPT
EXECUTE AS CALLER
AS
$$
snowflake.execute({sqlText: `USE DATABASE identifier('${DB_NAME}')`});
var schema_rows = snowflake.execute({
sqlText: `SELECT SCHEMA_NAME FROM INFORMATION_SCHEMA.SCHEMATA WHERE SCHEMA_NAME <> 'INFORMATION_SCHEMA'`
});
var discovered = [];
var granted = [];
while (schema_rows.next()) {
var schema = schema_rows.getColumnValue(1);
discovered.push(schema);
var futureGrants = snowflake.execute({sqlText: `SHOW FUTURE GRANTS IN SCHEMA "${schema}"`});
if (futureGrants.getRowCount() > 0) {
snowflake.execute({sqlText:`GRANT REFERENCES ON ALL TABLES IN SCHEMA "${schema}" TO ROLE identifier($revefi_role_name)`});
snowflake.execute({sqlText:`GRANT REFERENCES ON FUTURE TABLES IN SCHEMA "${schema}" TO ROLE identifier($revefi_role_name)`});
snowflake.execute({sqlText:`GRANT REFERENCES ON ALL VIEWS IN SCHEMA "${schema}" TO ROLE identifier($revefi_role_name)`});
snowflake.execute({sqlText:`GRANT REFERENCES ON FUTURE VIEWS IN SCHEMA "${schema}" TO ROLE identifier($revefi_role_name)`});
granted.push(schema);
}
}
return `discovered_schemas=[${discovered}], granted_schemas=[${granted}]`;
$$
;
-------------------------------------------------------------------------------
-- Loop through all databases specified in database_list.
-- Perform:
-- 1) DB-level privilege grants
-- 2) Schema-level FUTURE grant fix
--
-- At the end, return a SUMMARY of all databases processed.
-------------------------------------------------------------------------------
DECLARE
db STRING;
dbs ARRAY;
results ARRAY;
db_result STRING;
schema_result STRING;
BEGIN
dbs := SPLIT($database_list, ',');
results := ARRAY_CONSTRUCT();
FOR i IN 0 TO ARRAY_SIZE(dbs) - 1 DO
db := TRIM(dbs[i]::STRING);
-- Track and log output of procedures
-- Set database context each time. The scripts below modify the database used.
USE DATABASE identifier($db_for_procedure);
db_result := (CALL GRANT_DB_PRIVILEGES(:db));
schema_result := (CALL GRANT_SCHEMA_REFERENCES_FOR_DB(:db));
results := ARRAY_APPEND(results, OBJECT_CONSTRUCT(
'database', :db,
'db_privileges', db_result,
'schema_privileges', schema_result
));
END FOR;
RETURN 'Privilege grant summary:\n' || ARRAY_TO_STRING(results, ';\n');
END
;Step 3: Provide permissions to analyze query performance and view Warehouse configurations
- Revefi requires the MONITOR privilege on Snowflake warehouses to analyze queries for performance bottlenecks and provide optimization recommendations.
- The USAGE privilege is needed to view the Snowflake warehouse parameters. Revefi will only use a single warehouse (from Step 1) for all queries.
Please run the below script to grant this privilege to Revefi on a per Snowflake warehouse basis:
-- Use any existing database name that your current role has access to, this is only used to temporarily create the stored procedure below
SET db_for_procedure='<any_database>';
-- Manually grant permissions to one warehouse at a time using:
-- GRANT MONITOR ON WAREHOUSE <warehouse_name> TO ROLE identifier($revefi_role_name)
-- GRANT USAGE ON WAREHOUSE <warehouse_name> TO ROLE identifier($revefi_role_name)
--
-- To grant the permission for all your warehouses together:
USE DATABASE identifier($db_for_procedure);
CREATE OR REPLACE PROCEDURE GRANT_WAREHOUSE_PRIVILEGES_TO_REVEFI()
RETURNS VARCHAR
LANGUAGE javascript
EXECUTE AS CALLER
AS
$$
var warehouses_to_grant = snowflake.createStatement({ sqlText:`SHOW WAREHOUSES`}).execute();
var granted_warehouses = "";
while(warehouses_to_grant.next()) {
warehouse_name = warehouses_to_grant.getColumnValue("name");
snowflake.createStatement({ sqlText:`GRANT USAGE ON WAREHOUSE "${warehouse_name}" TO ROLE identifier($revefi_role_name)`}).execute();
snowflake.createStatement({ sqlText:`GRANT MONITOR ON WAREHOUSE "${warehouse_name}" TO ROLE identifier($revefi_role_name)`}).execute();
granted_warehouses += warehouse_name + ", "
}
return `Granted monitor and usage on warehouses: [${granted_warehouses}]`;
$$;
-- Invoke the procedure and clean up
CALL GRANT_WAREHOUSE_PRIVILEGES_TO_REVEFI();
DROP PROCEDURE GRANT_WAREHOUSE_PRIVILEGES_TO_REVEFI();Step 4: Provide permissions to MONITOR USAGE ON ACCOUNT
This is an optional step. Run this only if Revefi will monitor all tables across all your databasesThis permission gives Revefi the ability to see the configuration settings of future warehouses as well.
-- Allow Revefi to view all database names and the configuration settings of all
-- current and future warehouses
GRANT MONITOR USAGE ON ACCOUNT TO ROLE identifier($revefi_role_name);Step 5: Warehouse Management Privileges (Optional)
This is an optional step. This is needed by Revefi to manage and execute warehouse recommendations.Revefi uses Snowflake task to execute warehouse recommendations.
Run the below script to create a dedicated DB for revefi to store tasks and procedures needed for warehouse recommendations:
SET revefi_db='REVEFI_DB';
USE DATABASE identifier($revefi_db);
-- Grant permissions to create procedure and tasks in revefi_db
GRANT CREATE PROCEDURE ON SCHEMA PUBLIC TO ROLE identifier($revefi_role_name);
GRANT CREATE TASK ON SCHEMA PUBLIC TO ROLE identifier($revefi_role_name);
GRANT EXECUTE TASK ON ACCOUNT TO ROLE identifier($revefi_role_name);Run the below script to grant Revefi permissions to modify a warehouse's size:
-- To give permissions to selected warehouses one at a time, run the following command with warehouse name replaced
-- GRANT MODIFY ON WAREHOUSE <warehouse_name> TO ROLE identifier($revefi_role_name);
-- GRANT OPERATE ON WAREHOUSE <warehouse_name> TO ROLE identifier($revefi_role_name);Alternatively, grant Revefi permissions to modify all warehouses:
-- To grant the permission for all your warehouses together:
CREATE OR REPLACE PROCEDURE GRANT_WAREHOUSE_AUTO_MANAGEMENT_PRIVILEGES_TO_REVEFI()
RETURNS VARCHAR
LANGUAGE javascript
EXECUTE AS CALLER
AS
$$
var warehouses_to_grant = snowflake.createStatement({ sqlText:`SHOW WAREHOUSES`}).execute();
var granted_warehouses = "";
while(warehouses_to_grant.next()) {
warehouse_name = warehouses_to_grant.getColumnValue("name");
snowflake.createStatement({ sqlText:`GRANT MODIFY ON WAREHOUSE "${warehouse_name}" TO ROLE identifier($revefi_role_name)`}).execute();
snowflake.createStatement({ sqlText:`GRANT OPERATE ON WAREHOUSE "${warehouse_name}" TO ROLE identifier($revefi_role_name)`}).execute();
granted_warehouses += warehouse_name + ", "
}
return `Granted modify and operate on warehouses: [${granted_warehouses}]`;
$$;
-- Invoke the procedure and clean up
CALL GRANT_WAREHOUSE_AUTO_MANAGEMENT_PRIVILEGES_TO_REVEFI();
DROP PROCEDURE GRANT_WAREHOUSE_AUTO_MANAGEMENT_PRIVILEGES_TO_REVEFI();Additional security considerations
-
Allowlist Revefi IP addresses (if applicable)
Add Revefi IP addresses (44.225.56.55, 44.227.173.42, 52.10.141.35) to your Snowflake account if Snowflake is configured to only allow connections from an "allowed list" of IP addresses. -
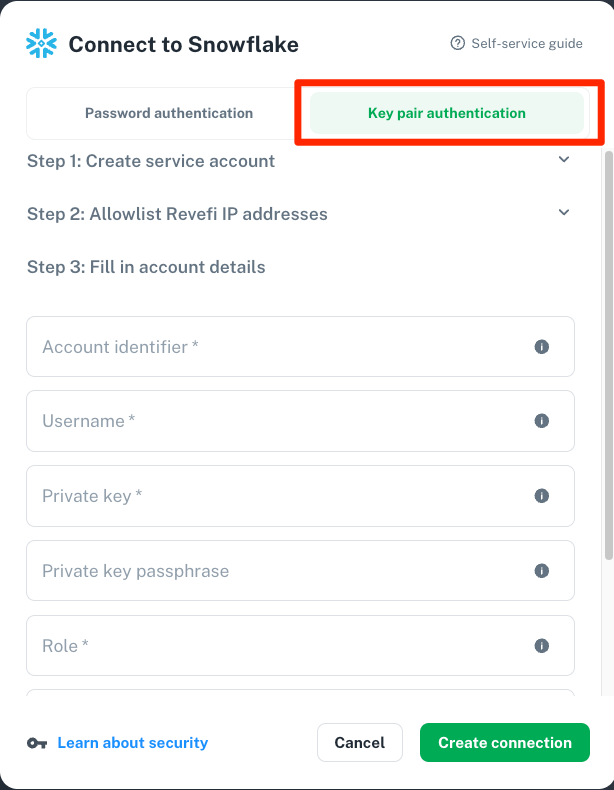
Snowflake recommends using key pair authentication for enhanced authentication security as an alternative to basic authentication (i.e. username and password). If you enable that for the user you use for Revefi monitoring, then follow the "Key pair authentication" path in the Connect to Snowflake page in Revefi. If you use encrypted private key, then make sure to fill in the Private key passphrase, otherwise leave that field blank for unencrypted private key.
Identify the account identifier using these steps.
- Snowflake will not support basic authentication (i.e username and password) starting Nov 2025. Revefi highly discourage the use of basic authentication for Snowflake connection.
FAQ
- The
CREATE OR REPLACE PROCEDURE GRANT_SCHEMA_REFERENCES_TO_REVEFI()statement creates the procedure under the chosen database's PUBLIC schema. If the database does not have a PUBLIC schema, you may see an error. In this case, simply select another schema in the database (either with theUSE SCHEMAcommand or from the Snowflake Worksheet UI) and re-run the script. - The
CALL GRANT_SCHEMA_REFERENCES_TO_REVEFI();statement requires a warehouse to be selected in the Snowflake Worksheet UI. This can be any warehouse that you have access to - not restricted to the warehouse created earlier. - In Step 2, for database names with special characters, please double quote the name. For e.g.
set database_name = '"prod-orders"'.
Finding your Snowflake Account ID
The best way to identify account identifier is through Snowsight or SQL.
Snowsight
- Open the account selector and review the list of accounts that you previously signed in to.
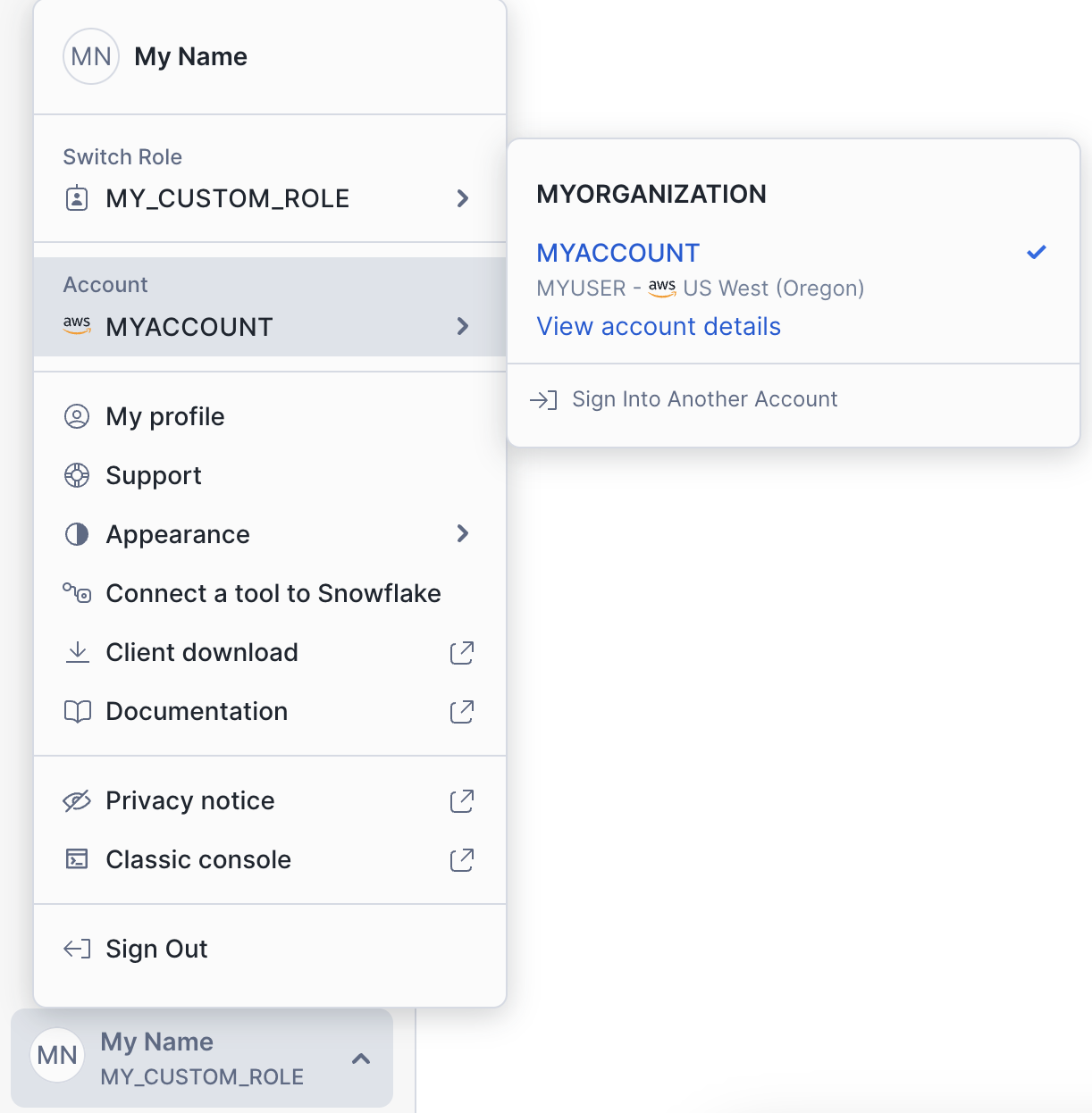
- Select View account details.
The Account Details dialog displays information about the account, including the account identifier and the account URL.
Using SQL
Execute this SQL query to get the account identifier.
SELECT CURRENT_ORGANIZATION_NAME() || '-' || CURRENT_ACCOUNT_NAME();Example Account Identifiers
Typically account identifier is the first part of your login URL, which looks like <account_identifier>.snowflakecomputing.com
Sample formats of account identifier
| Format | Account Identifier |
|---|---|
<account_locator>.snowflakecomputing.com | xy12345 |
<account_locator>.<cloud_region_id>.<cloud>.snowflakecomputing.com | xy12345.us-east-2.aws |
<orgname>-<account_name>.snowflakecomputing.com | acme-abc6789 |
For more information, visit https://docs.snowflake.com/en/user-guide/admin-account-identifier
Updated 24 days ago
Once you have run this Snowflake script, go to the Connections page in Revefi on the left nav, and click Connect on the Snowflake box to enter the credentials for the Revefi user created above! Once that's done, optionally set up to receive your alerts via Slack (default is your email).
